Security company Aqua Nautilus has exposed the RepoJacking vulnerability in GitHub libraries, which can be used by hackers to break into GitHub’s private or public libraries and replace files in these organizations’ internal environments or customer environments with versions of malicious code to carry out hijacking attacks.
RepoJacking, which can occur when a GitHub user/organization changes its name, is a supply chain attack that allows an attacker to take over dependencies or entire projects of GitHub projects to run malicious code against any device that uses those projects.
Hackers can directly scan the Internet, lock the GitHub library that needs to be attacked, and bypass the GitHub repository restrictions, replace the file with a version with a Trojan virus, and after other users download and deploy, hackers can manipulate the user terminal and carry out attacks.

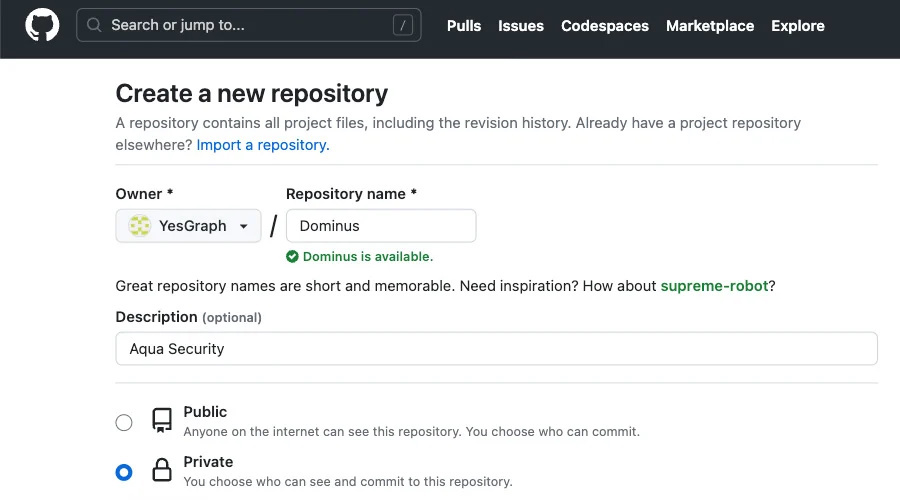
Aqua Nautilus uses Lyft for a demonstration, they create a fake repository, and get the script redirected, users using the install.sh script will unknowingly install Lyft with malicious code on their own, as of press time, Lyft’s vulnerability has been fixed.
The researchers also found related vulnerabilities in Google’s libraries on GitHub:
When users visit https://github.com/socraticorg/mathsteps, will be redirected to https://github.com/google/mathsteps so that the end user, Google will be given to the repository. However, because the socraticorg organization is available, the attacker can open the socraticorg/mathsteps repository and the user, if he executes the installation command given by Google directly in the terminal, will actually download the malicious files replaced by the hacker.
After feedback from Aqua Nautilus, Google has now fixed the issue.
Aqua Nautilus says that users can circumvent the RepoJacking vulnerability by creating a link between the old name of the GitHub library and the new name (redirecting the old name to the new name), which can be found here for more information.









